Bojana Dobran is the Product Marketing Manager at phoenixNAP.
When even a small business is a hot target for hackers, no organization can afford to be at risk.
In a recent survey by Ponemon and Keeper, 40% of US businesses said they experienced a cyber-attack. The report also reveals that the average cost of disruption to business operations increased from $1.21 million in 2017 to $1.9 million last year. While the actual cost of compromise declined for the reported period, the total cost of recovery grew significantly.
When it comes to small and medium-sized businesses, they too are seeing increased costs of disruption due to cyber-attacks. Some estimate that such companies lose between $8,000 and $74,000 per a single hour of downtime.
While these figures are significantly lower than those in the enterprise segment, they certainly point to the need for advanced cybersecurity solutions for businesses of all shapes and sizes. Yet, the challenge for small and medium-sized organizations remains the lack of personnel and financial resources to implement these solutions.
Top Cybersecurity Challenges for Mid-Market Organizations
Despite the increased cybersecurity awareness and proliferation of security systems, most organizations lack resources and knowledge to deploy strong defense mechanisms. The Ponemon and Keeper report listed the following three as the top challenges to implementing security strategies:
- 77% of organizations lack security personnel to mitigate risks
- 55% do not have sufficient budget to implement security solutions
- 45% do not understand how to protect their data
With the global market estimated to hit 3.5 million unfilled cybersecurity jobs by 2021, it is understandable why companies struggle to find security personnel. This gap is also the reason why they lack education on how to protect and how to choose the right solution.
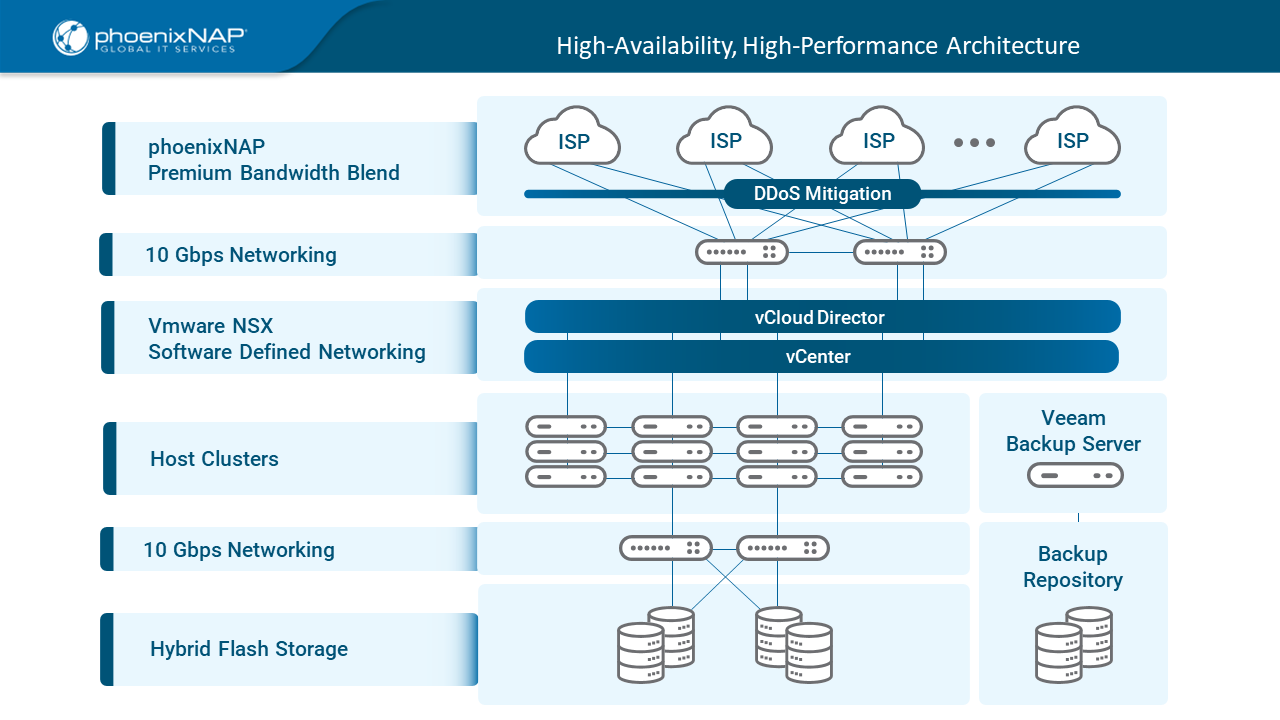
One way to overcome these challenges is to turn to specialized cloud-based security platforms such as Data Security Cloud (DSC), built by phoenixNAP and VMware. Available as an on-demand secure computing model, Data Security Cloud provides critical security resources at an affordable price point so that more small and medium-sized businesses can access it.
The platform is managed by certified security professionals, which eliminates the need for organizations to have in-house cyber security personnel or spend time and money on delivery and management of infrastructure. When it comes to its security features, one of its key components is VMware NSX, a network virtualization and security platform that adds a strong protection layer to virtualized environments.
VMware NSX in Data Security Cloud
By separating the network layer from hardware and integrating it with the hypervisor directly, VMware NSX forever changed the concept of software-defined networking (SDN). It made it possible for virtualized platforms to seamlessly integrate with protected networks and ensure greater security to underlying physical infrastructure.
Today, NSX is the industry’s leading solution for programmatic creation and management of software-based virtual networks. The reason for this is not only its usability and seamless integration with virtualized environments but also the advanced level of security it offers. Its micro-segmentation feature helps protect data across virtual machines and environments, allowing for greater workload mobility regardless of physical networks.
By segmenting the network from the hardware, NSX minimizes the attack vector on a network affecting the underlying hardware. Combined with hardware with in-built security features in phoenixNAP’s Data Security Cloud, NSX provided a basis for building the world’s most secure cloud-based platform.
NSX on Secure Hardware
While NSX ensures security on the network and VM level, hardware security is equally important to protect data at the core. This is why phoenixNAP deployed it on the 2nd Gen Intel Xeon Scalable processors, which have in-built security features and exceptional performance capabilities. As the latest generation data center architecture by Intel, these processors ensure that performance is not compromised for advanced security.
Working together to create a secure cloud platform, phoenixNAP, Intel, and VMware deployed industry leading technologies in a single solution, providing improved security and performance. In addition to this, the solution includes threat intelligence features, vulnerability scanning, and 24/7 available SOC team to provide comprehensive protection and compliance-readiness.
Delivered as an on-demand model, DSC requires no capex investments and can be deployed in a matter of hours with essential or advanced security components. Its cost-efficiency enables even small and mid-sized organizations to access enterprise-grade data protection technologies and meet their security and compliance goals.
For more information about the solution, visit Data Security Cloud page or download a free e-book Anatomy of a Secure Cloud Service.

